SharePoint User A authenticated as User B
09/05/2018 Leave a comment
How could that happen ?
Let me give a some information about the problem:
Issue:
Intermittently Users authenticated with reverse proxy, impersonate incorrectly and User A may become User B . Based on user privileges , end users experiencing either access denied or having different user identity and permissions.
Receipts
- 1 In the middle Device ,who redirects authentication or re-authenticate. (I am not meaning a hacker device , if you are using SSL, it is not possible easily but your system admins can). It is mostly a Reverse Proxy configured officially by your system admins.All most every modern proxy has a feature that uses Port Sharing or Re-use Session functionality. It is perfectly fine , provides high performance , prevent reauthentication and port exhaustion problem.It is works for well almost every scenario . Almost!!!
- Session-Based Authentication , (Like NTLM or Certificate Authentication). In our scenario,We have one web application with two Authentication Provider , 1 for default CBA/NTLM and 1 for CBA/Form-Based Authentication. (Issue happens on CBA/NTLM part)
- This configuration provides another authentication layer on SharePoint ,and force SharePoint to use Federated Authentication mechanizm , so you will see Fed Auth cookies are in use.
Some important information:
Federated Authentication over CBA/NTLM. Despite the fact that it is a token/cookie based architecture, it is depending on NTLM authentication under the cover. It means it is still a Session Based Authentication.
Why we have a problem:
Because Any middle device setting for “same TCP session re-use” is not suitable/unsupported for any “Session Based” authentication type.
The issue, It is not related directly SharePoint implementation , It is related that how the Session Based Authentication works.
Also same problem may occur ; faulty middle device software and other incorrect configurations.
How the issue happens,
Lets have a look in details for Federated Authentication over CBA/NTLM.
In TCP/Network Layer – We don’t have any authentication in this layer.
We have two end points . Point A (Reverse Proxy) to Point B (SharePoint WFE)
Before autentication a TCP connection estabilishes between that two points.
Example
Point A – IP 10.10.0.5 , Source Port : 45000 -> Point B – IP : 10.10.0.25 port 443
We are now calling this “A TCP Channel” or “A TCP Session” .
After TCP connection is estabilished then HTTP start to work in that channel.
HTTP Layer
User go to the server anymously first , the server provides authentication challanges it supported. And user provides its credential assets . This is called NTLM Handshake;


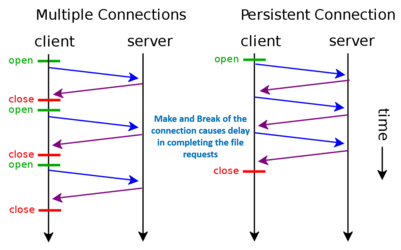
TCP Channel should not closed until NTLM handshake complete. It is a requirement for
NTLM authentication . Thats why , all modern web servers , use a standart/feature called HTTP Keep Alive which provides “Persistent Connection” not only NTLM handshake duration , also several requests are handled in same TCP Channel until Client or Server close the connection.
After NTLM HandShake completed , IIS Stores the Session Information ,
TCP Channel X -> [Point A] [IP], [Port] <=> Identity : Authenticated User A. (Or Anonymous)
(If we don’t use , HTTP Keep Alive, For every request we need to do re-authenticate . (it is not a session based authentication it is called Request Based Authentication . Well NTLM fails in that scenario. You will see flooding 401 responses on NTLM handshake.)
CBA/NTLM
Now SharePoint come in the scenario , It builds claims and tokens on IIS/NTLM Identity , creates the tokens via Security Token Service , caches the tokens with Distributed Cache or Local Cache.
SharePoint and IIS believe and trust , underlayer TCP Session belong to only one verified authenticated identity.
If you have more than one authentication provider , SharePoint also builds Federated Authentication Cookies , default 5 days duration .Cookie – Token pairs must be match for user verification.
Fed Auth Cookie sent to client with last response in NTLM handshake (Status 200 or 302).
and corresponding Token has been cached in server (default 10 hours).
All incomming requests are considered valid/authenticated based on Fed Auth Cookie – Security token pair.
What happens if SharePoint can’t find token in the cache:
If the cookie valids , It rebuilds the token and cache the token again and updates the cookie. (You will have another 5 days, “sliding” )
It do not re-authenticate.
What happens if the Cookie expires: Well you need to reauthenticate.
What happens if the TCP Channel closed : you need to reauthenticate. But sometimes it is not happen! Even client send close channel , in the middle devices can prevent it. Because It wants to reuse that TCP Channel.
So far so good,
But what if someone , some other user use the same TCP Channel and send requests to the server . Well exactly what is happening if the reverse proxy does in session-reuse functionality.
SharePoint and IIS believe and trust , underlayer TCP Session belong to only one verified authenticated identity.Because how the bible says for Session-Based Authentication works.
Problematic Scenario:
Lets assume User A authenticated , have a valid cookie and continue communication without re-autheticate using Cookie-Token pairs for validation.
In mean while User B make a request (anonymous first) from same TCP Channel and requesting authentication.It is NTLM. Well the TCP Channel is not closed , it is the same channel, There is no possibility to understand it is the different user, Server reuthenticate the user.
After NTLM HandShake completed , IIS Stores the Session Information by overriding ,
TCP Channel X -> [Point A] [IP], [Port] <=> Identity : Authenticated User B. (Or Anonymous)
IP is the always Reverse proxy it isn’t changed.Also we have using the same TCP Channel so the port also same. It is absolute override.
Now the channel is belong to USER B instead of USER A.
Well User A still have no issues, he has a valid cookie and we have a valid token , so User A and User B communicates with the server without any problem in same tcp channel.
But the problem happen when the token is missed/expired (default 10 hours) .
What SharePoint does , verify the channel in that point ,ask to the IIS what was the Identity ? IIS tells : it is UserB . SharePoint recreates the token and updates the cookie for UserB in a request which belong to UserA.
Now User A gets inccorect cookie and have inccorect token cached . It becomes User B by now.
Depends on permissions , either facing access denieds or have access UserB’s resources.
This problem is called “Session Hijacking“.
This is not a security hole in Sharepoint ,IIS or NTLM .
An anology :
Lets assume , you have a internet faced web site under authentication have must protected resources and if you enable anonymous access on that server in same resources .Is it considered security hole in authentication mechanizm or your code ? Of course not.
Well, there is still a security issue because of unsupported or incorrect configuration . Also it is not depended on Sharepoint, It may happen any ASP.NET application on any kind of Session-Based Authentication.
In conclusion,
Any “Session Based” authentication (like NTLM, Certificate auth etc.) to work needs one TCP Channel per authenticated user.
SharePoint Federated Authentication for Claims Based Authentication over NTLM is depending on the underlying NTLM Authentication. NTLM is a session based authentication . Any middle device setting for “same TCP session re-use” is not suitable/unsupported for these type of authentications.
Suggestions:
- Disabling “TCP Channel/Session re-use” feature in middle devices
- Update in the middle devices firmware for any faulty software
- Not using Session-Based Authentication with Reverse Proxy “Session re-use” feature or changing authentication type for any/suitable “Request-based” authentication or “token based” authentication (like ADFS) or Form based authentication.
Note: Don’t mess with “Session ” that is TCP level Session/Channel, not an application level session object or structure !! (OSI Layer 5)
